Holistic GRC services, consulting, and audit for your ERP security
Ensure that your most important systems and data are protected: We offer tailored services for governance, risk and compliance. From audits and consulting to control systems – we steer you purposefully through stormy times.
Solutions for our clients
Which solutions we have implemented in which industries: Focus on strong implementation.
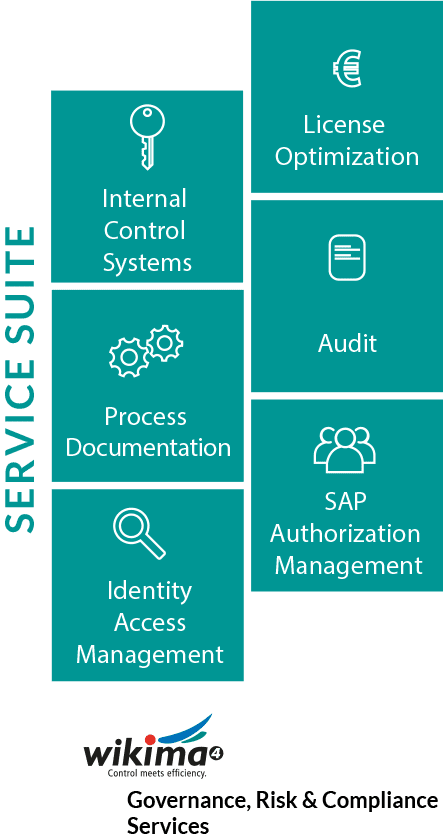
GRC Service Suite from wikima4
As GRC experts, we support our customers with our services.
Service packages at a fixed price
We offer service packages at a fixed price: to get to know each other or to deepen cooperation.
IN PRACTICE
Goals and implementation for more security in different industries
Continuous
Compliance monitoring
Identity Management
Concept for internal control system (“ICS”)
wikima4
Customer Success Story

GRC Services Suite
Transparent processes, structures that cover the entire value chain and automated reporting are the prerequisites for any company to meet the high demands for compliance and the challenge of “IT security” in a holistic manner.
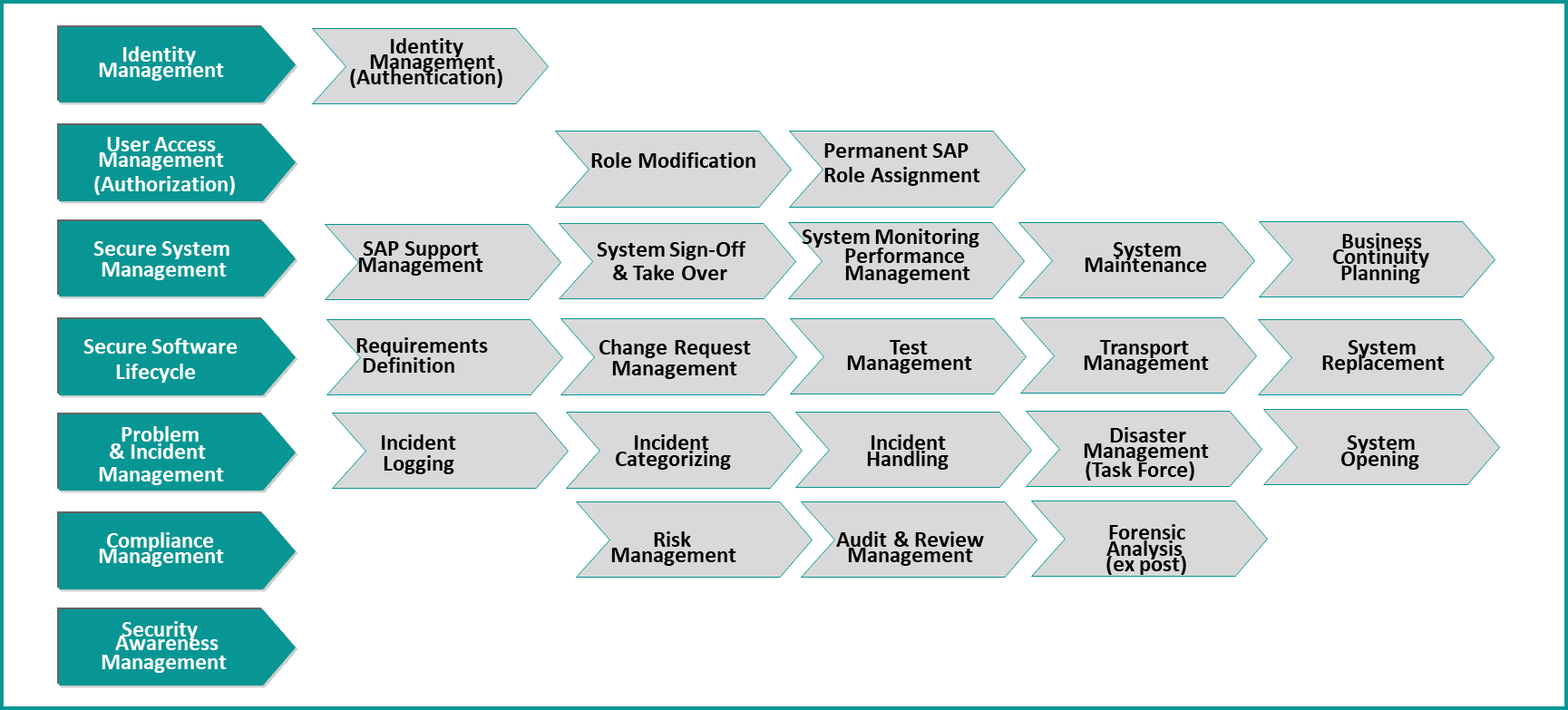
We successfully apply the following principles in our GRC customer projects:
- We make project goals measurable right from the start with KPIs (key performance indicators).
- We use organisational attributes from organisational management in HR to build up (partial) automation.
- Our templates are adapted to the client’s individual objectives. Client-internal results are assessed and added to the templates.
- We go step by step into the technical and business implementation.
- We use internal and external project management in a sensible and resource-saving way.
From our many years of expertise and in cooperation with our clients, we have developed specific GRC services in 6 areas.
Internal Control Systems (ICS)
Creation and implementation of internal control systems
System hygiene

Identity Access Management Services (IDM)
User Access Management
wikima4 Template SAP Roles
Licence Optimisation
Cost-efficient asset distribution (licences)
Usage and demand forecasts
Audit Services
Competence for internal compliance and security tasks
Reporting for management
Process documentation
Transparency of business processes and controls
Business Process Excellence

SAP Authorization Management
Conceptual guideline for content-related authorisation roles
Basis for switching to new technologies
GRC Service packages for SME at a fixed price
SAP NetWeaver Identity Management
Would you like a detailed insight into the functional possibilities and benefits of SAP NetWeaver Identity Management?
wikima4 creates a proof-of-concept for your company with which you can design provisioning in SAP landscapes in a simple, secure, efficient and audit-compliant manner.
Please contact us directly dor a proof of concept for enterprise.
Package price
EUR 7’900
excluding travel expenses, excluding VAT
Our approach
Day 1:
Kick-off workshop on-site presentation of SAP NetWeaver Identity Management, clarification of the customer situation and recording of general requirements
Day 2:
Installation of SAP NetWeaver Identity Management on a test server provided by you (remote).
Day 3 & 4:
Setting up the exemplary scenarios for the typical identity management functions (remote)
Day 5:
Review workshop in your company: Summary of the results, training of the users, definition of the next steps.
Well-being package SAP Compliance & Security
The feel-good package “SAP Compliance & Security” accompanies you and your company in this task. We answer these questions with analyses and audits in workshops and personal discussions:
- What conflicts currently exist when accessing data in SAP?
- What organizational and technical measures are required to ensure SAP compliance?
- How can these measures and processes be implemented in the company in such a way that they are accepted by employees and become part of the corporate DNA?
Get to know price
EUR 12’300
excluding travel expenses, excluding VAT
Project steps
- System hygiene
Review of roles and users for their activities Analysis of which roles, users and licenses can be further maintained or eliminated. - Conflict and cost analyses
SAP roles are checked for conflicts, measures are defined. User cleansing shows potential savings in license costs. - Snapshot «Audit»
3.1. “Segregation of Duties” conflicts: Critical authorization assignments are analyzed and addressed in joint workshops.
3.2. “General IT Controls”: Areas for which the CIO is responsible are analyzed and jointly addressed. - Process landscape
Design of optimized processes and integration into the organization for identity access management are jointly developed and introduced in the company.
